Resetting the system management controller (SMC) can resolve certain issues related to power, battery, fans, and other features.
Reset the SMC on computers that have the T2 chip
If your Mac has the Apple T2 Security Chip, follow these steps. If you need help, contact Apple Support.
Notebook computers with the T2 chip
Before resetting the SMC, try these steps:
- Shut down your Mac.
- Press and hold the power button for 10 seconds, then release the button.
- Wait a few seconds, then press the power button to turn on your Mac.
If the issue persists, follow these steps to reset the SMC:
- Shut down your Mac.
- On your built-in keyboard, press and hold all of the following keys. Your Mac might turn on.
- Control
 on the left side of your keyboard
on the left side of your keyboard - Option (Alt)
 on the left side of your keyboard
on the left side of your keyboard - Shift
 on the right side of your keyboard
on the right side of your keyboard
- Control
- Keep holding all three keys for 7 seconds, then press and hold the power button as well. If your Mac is on, it will turn off as you hold the keys.
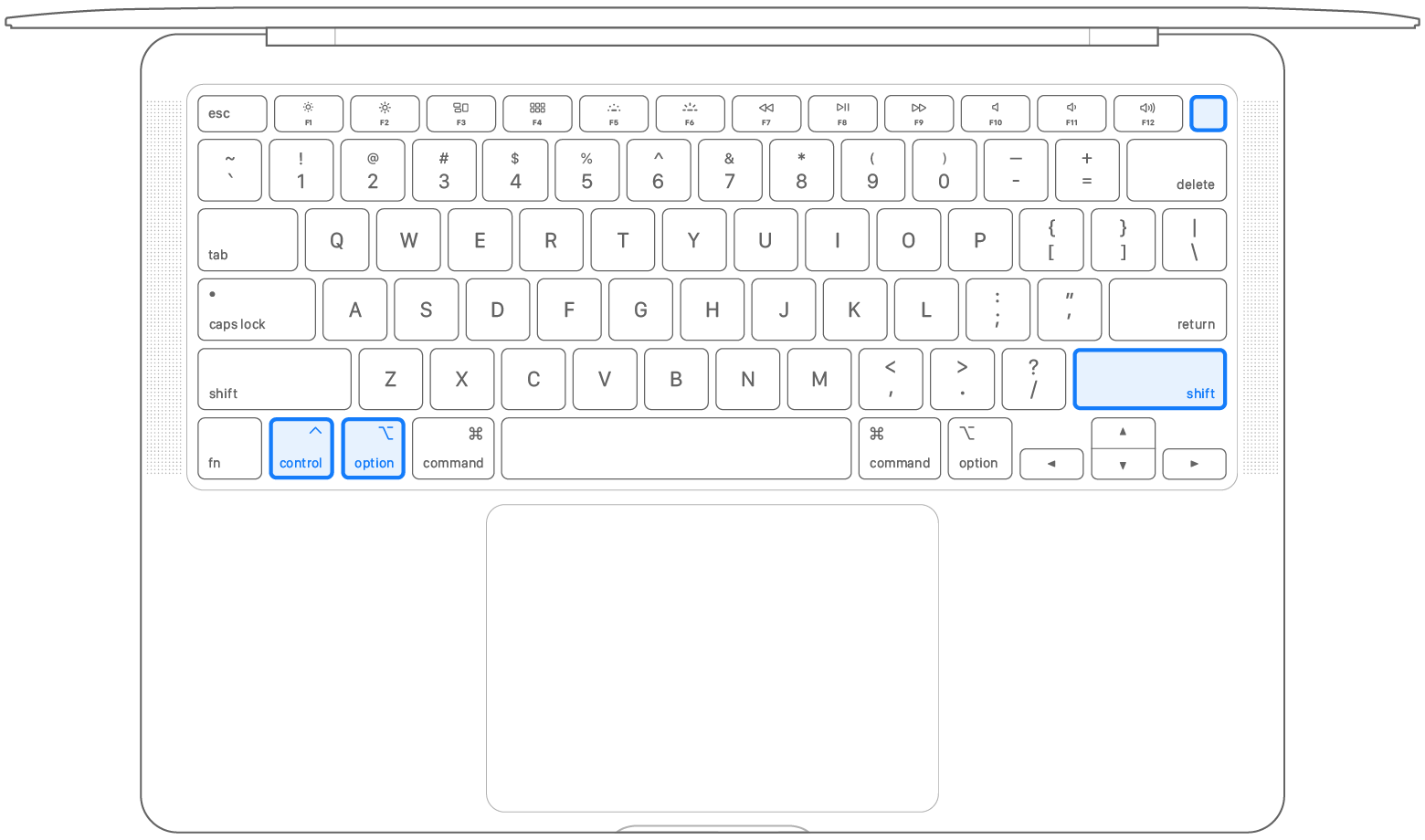
- Keep holding all four keys for another 7 seconds, then release them.
- Wait a few seconds, then press the power button to turn on your Mac.
Desktop computers with the T2 chip
- Shut down your Mac, then unplug the power cord.
- Wait 15 seconds, then plug the power cord back in.
- Wait 5 seconds, then press the power button to turn on your Mac.
Comments
Post a Comment
https://gengwg.blogspot.com/