Switched Fabric or switching fabric is a network topology in which network nodes interconnect via one or more network switches (particularly crossbar switches). Because a switched fabric network spreads network traffic across multiple physical links, it yields higher total throughput than broadcast networks, such as the early 10BASE5 version of Ethernet, or most wireless networks such as Wi-Fi.
The generation of high-speed serial data interconnects that appeared in 2001–2004 which provided point-to-point connectivity between processor and peripheral devices are sometimes referred to as fabrics; however, they lack features such as a message passing protocol.[citation needed] HyperTransport, for example, continues to maintain a processor bus focus even after adopting a higher speed physical layer. Similarly, PCI Express is just a serial version of PCI; it adheres to PCI’s host/peripheral load/store DMA-based architecture on top of a serial physical and link layer.
Fibre Channel[edit]
In the Fibre Channel Switched Fabric (FC-SW-6) topology, devices are connected to each other through one or more Fibre Channel switches. While this topology has the best scalability of the three FC topologies (the other two are Arbitrated Loop and point-to-point), it is the only one requiring switches, which are costly hardware devices.
Visibility among devices (called nodes) in a fabric is typically controlled with Fibre Channel zoning.
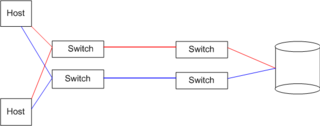
Multiple switches in a fabric usually form a mesh network, with devices being on the "edges" ("leaves") of the mesh. Most Fibre Channel network designs employ two separate fabrics for redundancy. The two fabrics share the edge nodes (devices), but are otherwise unconnected. One of the advantages of such setup is capability of failover, meaning that in case one link breaks or a fabric goes out of order, datagrams can be sent via the second fabric.
The fabric topology allows the connection of up to the theoretical maximum of 16 million devices, limited only by the available address space (224).

Comments
Post a Comment
https://gengwg.blogspot.com/