A license agreement accompanies open-source software and the related source code.
The license describes how the source code and the components built from it can be used and how any software created with it should deal with it.
According to the open-source definition of OpenSource.org, a license shouldn't:
- Discriminate against persons or groups.
- Discriminate against fields of endeavor.
- Be specific to a product.
- Restrict other software.
- And more - See the Open Source Definition.
To cover the exact terms of a license, several types exist. Each type has its specifics and implications, which we'll cover in the next part.
Even though multiple contributors generally develop open-source software from the community, it doesn't guarantee that it's secure and without vulnerabilities.
Multiple reviewers discover chances, but the discovery might not be immediate or before being consumed by others.
Since the source code is open-source, people with malicious intent can also inspect the code for vulnerabilities and exploit it when possible.
In that regard, it's both a blessing and a curse that open-source software has source code available for others.
Packages are the formalized ways to distribute software components.
The licensing types and concerns about vulnerabilities extend to the packages, as these contain the components.
Types of licenses
There are multiple licenses used in open-source, and they're different.
The license spectrum is a chart showing licenses from the developer's perspective and the implications of use for downstream requirements imposed on the overall solution and source code.
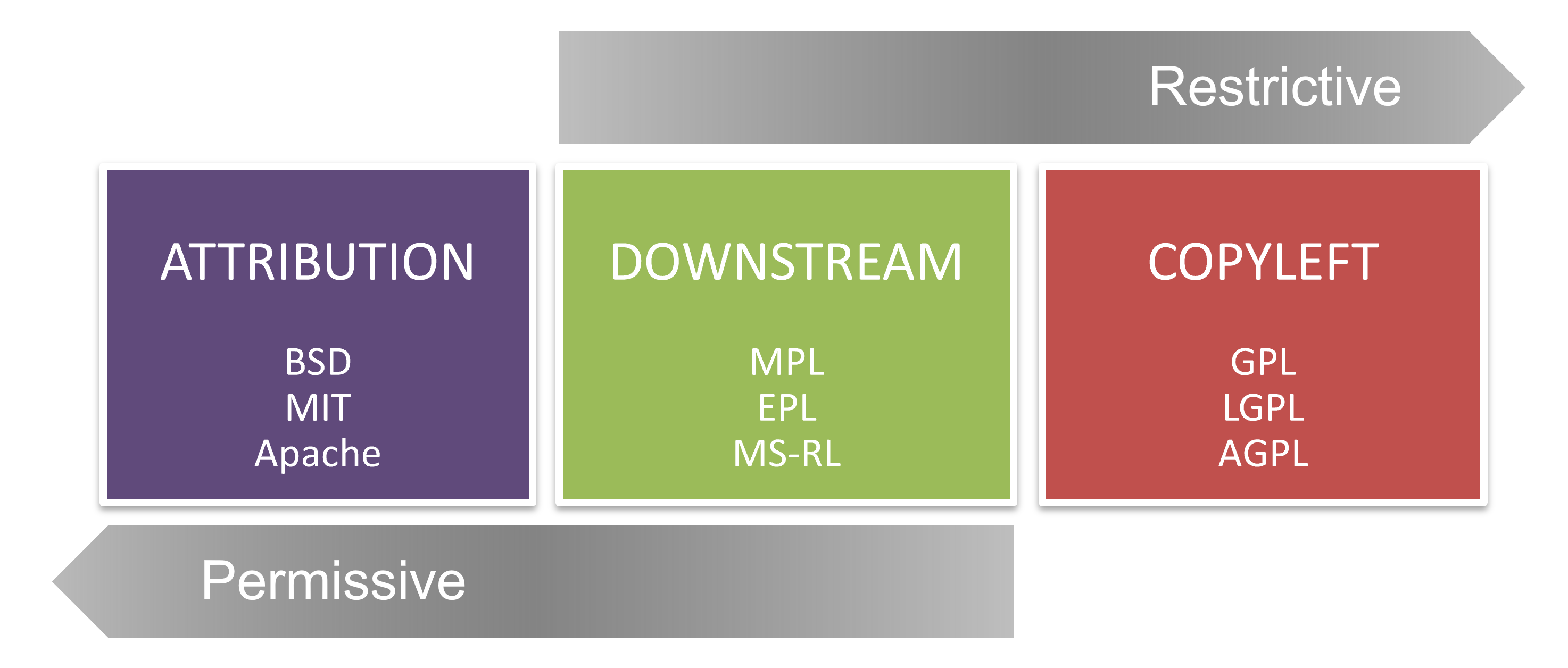
On the left side, there are the "attribution" licenses. They're permissive and allow practically every type of use by the software that consumes it. An example is building commercially available software, including the components or source code under this license.
The only restriction is that the original attribution to the authors remains included in the source code or as part of the downstream use of the new software. The right side of the spectrum shows the "copyleft" licenses.
These licenses are considered viral, as the use of the source code and its components, and distribution of the complete software, implies that all source code using it should follow the same license form.
The viral nature is that the use of the software covered under this license type forces you to forward the same license for all work with or on the original software.
The middle of the spectrum shows the "downstream" or "weak copyleft" licenses. It also requires that it must do so under the same license terms when the covered code is distributed.
Unlike the copyleft licenses, it doesn't extend to improvements or additions to the covered code.
Any form of software that uses code or components must consider the license type that is covered.
For companies, it becomes essential to know the types of licenses for components and packages that developers choose to use.
When these include even one viral license, it requires that all software uses the same license.
Any intellectual property you might have must be made public and open source according to the terms of the viral license type.
It has a tremendous impact on the project's source code and the company that produces it.
License rating
Licenses can be rated by the impact that they have. When a package has a specific type of license, the use of the package implies keeping to the requirements of the package.
The license's impact on the downstream use of the code, components, and packages can be rated as High, Medium, and Low, depending on the copy-left, downstream, or attribution nature of the license type.
For compliance reasons, a high license rating can be considered a risk for compliance, intellectual property, and exclusive rights.
Package security
The use of components creates a software supply chain.
The resultant product is a composition of all its parts and components.
It applies to the security level of the solution as well. So, like license types, it's essential to know how secure the components being used are.
If one of the components used isn't secure, then the entire solution isn't either.
Comments
Post a Comment
https://gengwg.blogspot.com/