Threat modeling is a core element of the Microsoft Security Development Lifecycle (SDL).
It's an engineering technique you can use to help you identify threats, attacks, vulnerabilities, and countermeasures that could affect your application.
You can use threat modeling to shape your application's design, meet your company's security goals, and reduce risk.
With non-security experts in mind, the tool makes threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models.
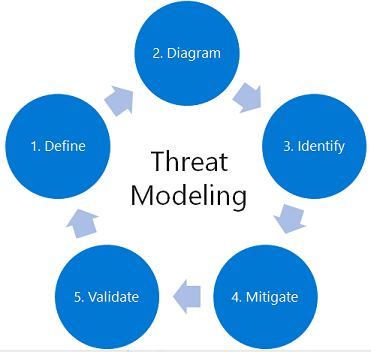
There are five major threat modeling steps:
- Defining security requirements.
- Creating an application diagram.
- Identifying threats.
- Mitigating threats.
- Validating that threats have been mitigated.
Threat modeling should be part of your typical development lifecycle, enabling you to refine your threat model and progressively reduce risk.
Microsoft Threat Modeling Tool
The Microsoft Threat Modeling Tool makes threat modeling easier for all developers through a standard notation for visualizing system components, data flows, and security boundaries.
It also helps threat modelers identify classes of threats they should consider based on the structure of their software design.
The tool has been designed with non-security experts in mind, making threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models.
The Threat Modeling Tool enables any developer or software architect to:
- Communicate about the security design of their systems.
- Analyze those designs for potential security issues using a proven methodology.
- Suggest and manage mitigation for security issues.
For more information, you can see:
Security can't be a separate department in a silo. It also can't be added at the end of a project.
Security must be part of DevOps, and together they're called DevSecOps.
The biggest weakness isn't knowing the flaw in your solution. Microsoft has created a threat modeling tool to remediate it, which helps you understand potential security vulnerabilities in your solution.
The Threat Modeling Tool is a core element of the Microsoft Security Development Life cycle (SDL).
It allows software architects to identify and mitigate potential security issues early when they're relatively easy and cost-effective to resolve.
As a result, it dramatically reduces the total cost of development.
The tool has been designed with non-security experts in mind, making threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models.
The tool enables anyone to:
- Communicate about the security design of their systems.
- Analyze those designs for potential security issues using a proven methodology.
- Suggest and manage mitigations for security issues.
Comments
Post a Comment
https://gengwg.blogspot.com/