Before diving into high-quality release pipelines, we must consider the difference between release and release processes. Or, when you talk about tooling, a release pipeline.
We start with defining a release process or release pipeline. The release pipeline contains all the steps you walk through when you move your artifact from one of the artifact sources discussed earlier through the stages or environments.
The stage can be a development stage, a test stage, a production stage, or a stage where a specific user can access the application.
Part of your pipeline is the people who approve the release or the deployment to a specific stage. Also, triggers or schedules on which the releases execute, and the release gates, the automatic approvals of the process.
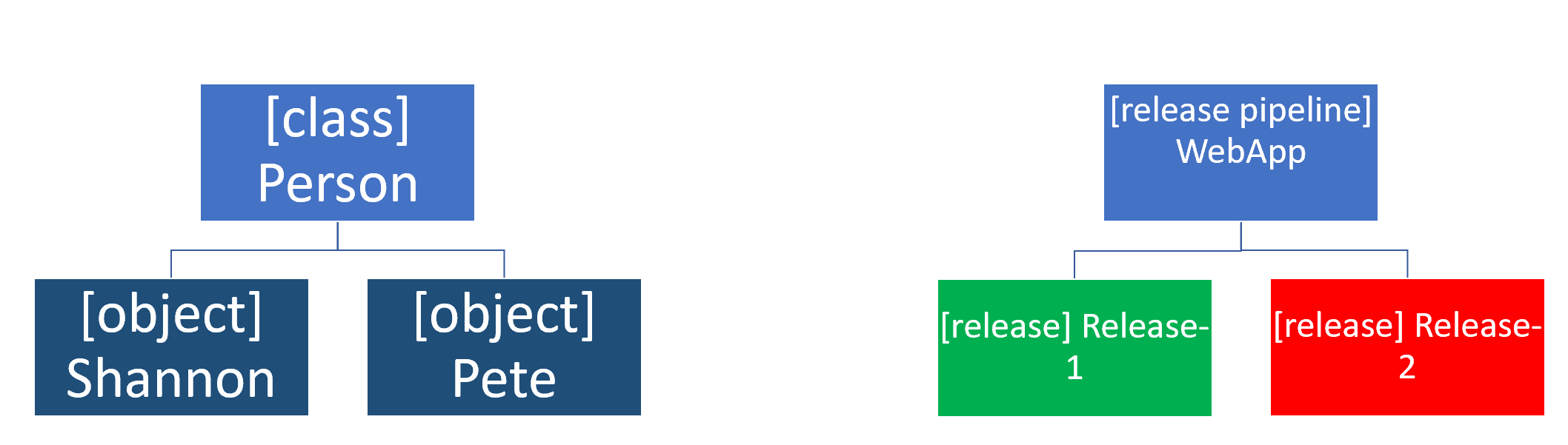
The release itself is something different. The release is an instance of the release pipeline. You can compare it with object instantiation.
In Object Orientation, a class contains the blueprint or definition of an object. But the object itself is an instance of that blueprint.
Comments
Post a Comment
https://gengwg.blogspot.com/