Packages contain components that are built from source code. Open-source code is publicly available for inspection, reuse, and contribution.
Most commonly, open-source projects indicate how the sources can be used and distributed afterward. A license agreement comes with the source code and specifies what can and cannot be done.
Software today is built by using components. These components are created in part by the team that is writing the entire software solution.
Some dependencies are on components created and made available by other teams, third-party companies, and the community. The packages that contain the components are a formalized way for distribution.
On average, the built software solution is around 80% based on existing components and maintained outside of the project.
The rest of the solution consists of your code with business logic and specifics for the functional requirements. Plus, "glue" code that binds the components and your code. The components can be a commercial offering or free of charge.
A considerable part of the publically available and free components are community efforts to offer reusable components for everyone to use and build software. The persons creating and maintaining these components often also make the source code available.
It's open-source code as opposed to closed source. A closed source means that the source code isn't available, even though components are available.
Wikipedia defines open-source software as follows:
"Open-source software is a type of computer software in which source code is released under a license in which the copyright holder grants users the rights to study, change, and distribute the software to anyone and for any purpose."
The related open-source software development is a collaborative form of software development involving multiple contributors. Together they create and maintain software and source code using open sources. The use of open-source software is widely adopted now.
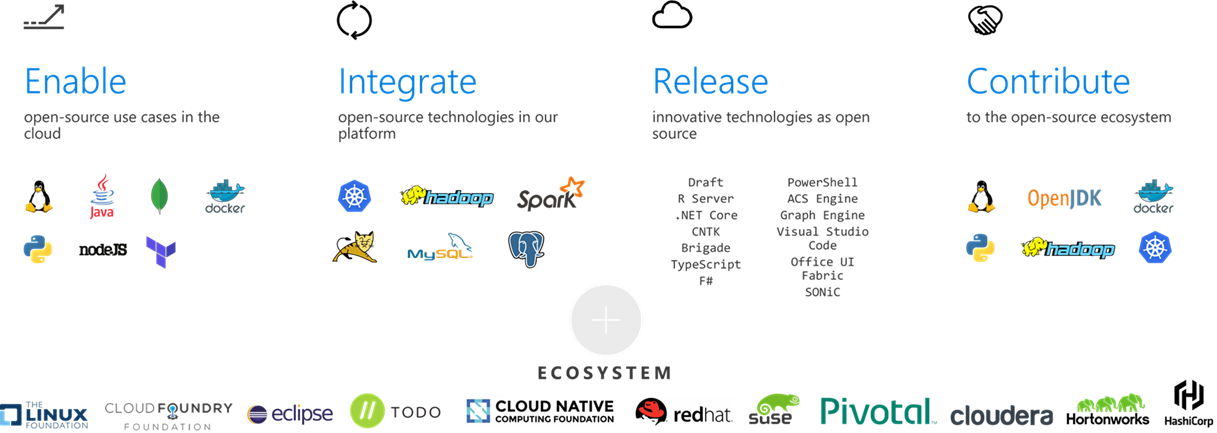
Microsoft itself has also-embraced open-source software in its software and the development platforms they offer.
The .NET platforms, such as the original .NET Framework and even more so .NET Core, use several components created by the open-source community and not Microsoft itself. In ASP.NET and ASP.NET Core, many of the frontend development libraries are open-source components, such as jQuery, Angular, and React.
Instead of creating new components themselves, the teams at Microsoft are using the open-source components and taking a dependency on them.
The teams also contribute and invest in the open-source components and projects, joining in on the collaborative effort. Besides adopting external open-source software, Microsoft has also made significant parts of its software available as open-source.
.NET is a perfect example of how Microsoft has changed its posture towards open source. It has made the codebase for the .NET Framework and .NET Core available and many other components.
The .NET Foundation aims to advocate the needs and evangelize the benefits of the .NET platform. And promote the use of .NET open source for developers.
For more information, see the .NET Foundation website.
In summary, modern software development, including the Microsoft developer platform and ecosystem, implies open-source components.
It has implications for companies that build software, either commercially or for internal use.
The inclusion of software components that are not built by the companies themselves means no complete control over the sources.
Being responsible for the source code used in components used within a company means that you must accept its risks. The concerns are that source code component:
- Are of low quality. It would impact the maintainability, reliability, and performance of the overall solution.
- Have no active maintenance. The code wouldn't evolve or be alterable without copying the source code, effectively forking away from the origin.
- Contain malicious code. The entire system that includes and uses the code will be compromised. Potentially the whole company's IT and infrastructure is affected.
- Have security vulnerabilities. The security of a software system is as good as its weakest part. Using source code with vulnerabilities makes the entire system susceptible to attack by hackers and misuse.
- Have unfavorable licensing restrictions. The effect of a license can affect the entire solution that uses the open-source software.
The companies will have to make a trade-off: its developers want to use open-source software components, allowing them to speed up development and use modern frameworks, libraries, and practices.
On the other hand, giving the developers and projects the freedom to include open-source software should not put the company at risk.
The company's challenges are finding a way to keep the developers empowered and free to choose technology to use while making sure the risks for the company are managed as well as possible.
Other challenges come from companies that offer open-source software to the public.
These challenges include having a business model around the open-source, when to publish open-source code and how to deal with community contributions.
The fact that your source code is open doesn't imply that anyone can make changes to it.
There can be contributions from community collaboration, but a company doesn't necessarily have to accept it. It's referred to as-closed open-source.
Suggestions for change are welcome, but the maintainers are the ones that carry out the actual changes.
Comments
Post a Comment
https://gengwg.blogspot.com/